How to set up sFTP for using Certificate Authentication on Linux
These instructions apply to users who are receiving their statements via sFTP. If you elected to receive your statements via sFTP, you would first need to generate an RSA Key pair.
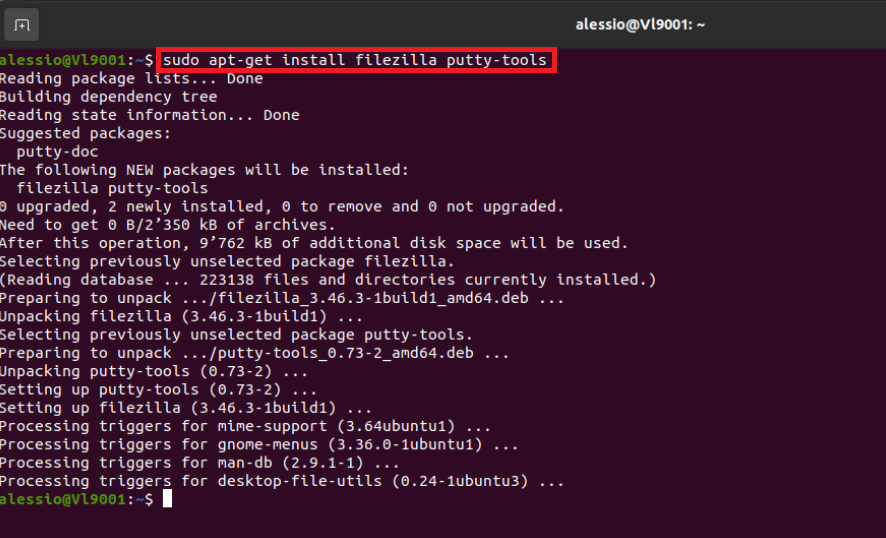
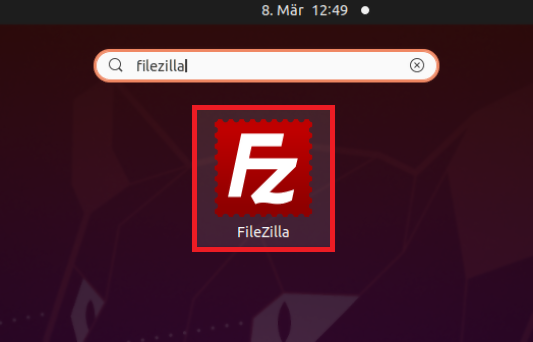
There are many Linux distributions and there are multiple methods to access the IBKR sFTP server. sFTP clients such as Filezilla can be used. In this article we explain how to realize the connection to the IBKR FTP server using Ubuntu Linux and Filezilla.
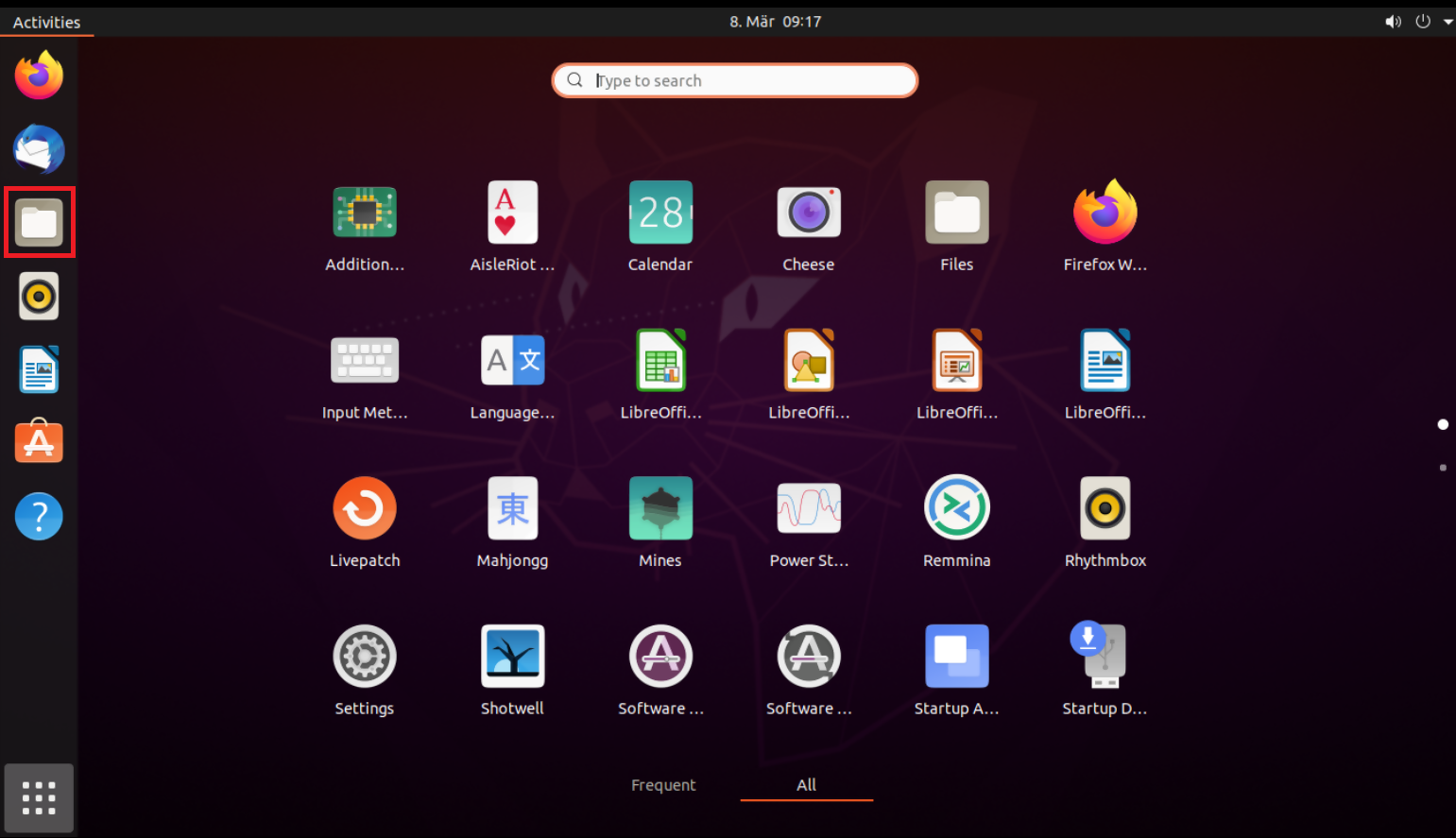
1. On your Linux machine, click on the Applications icon in the bottom left corner of you screen.

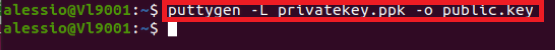
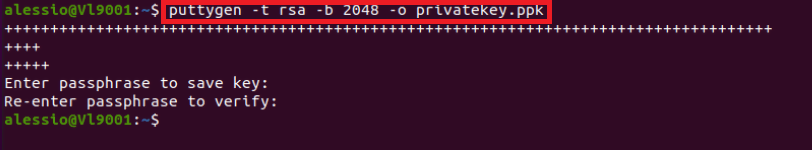
4. Once the software installation is complete, type puttygen -t rsa -b 2048 -o privatekey.ppk in order to generate the RSA Key pair.

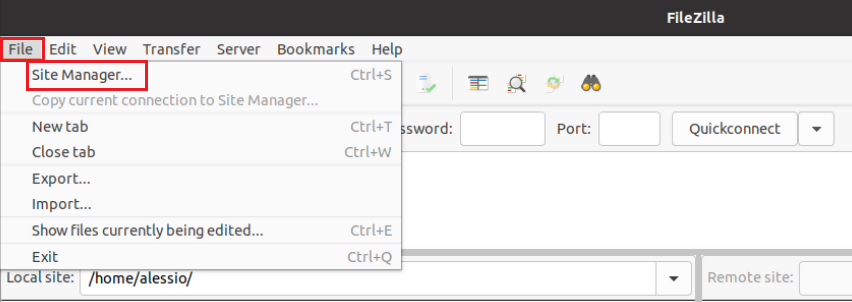
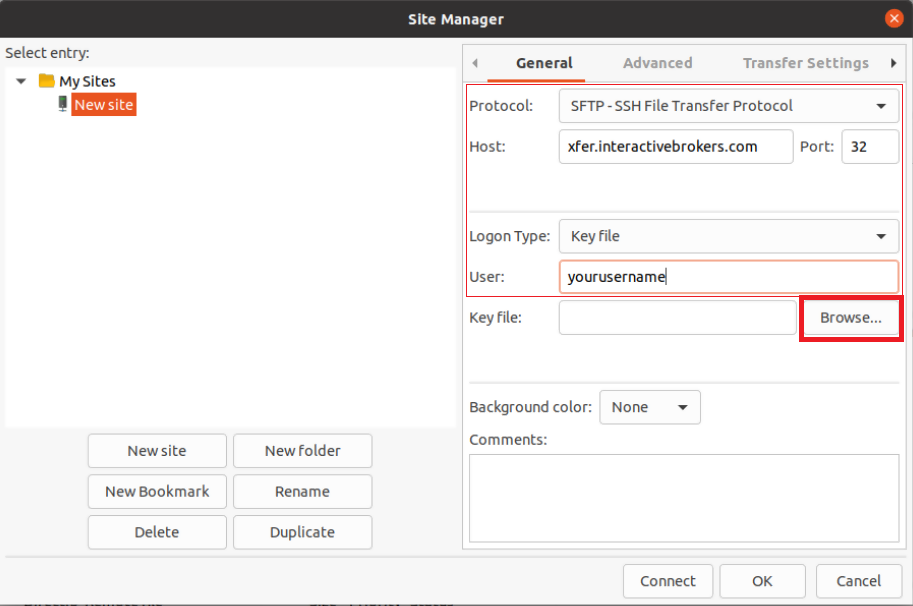
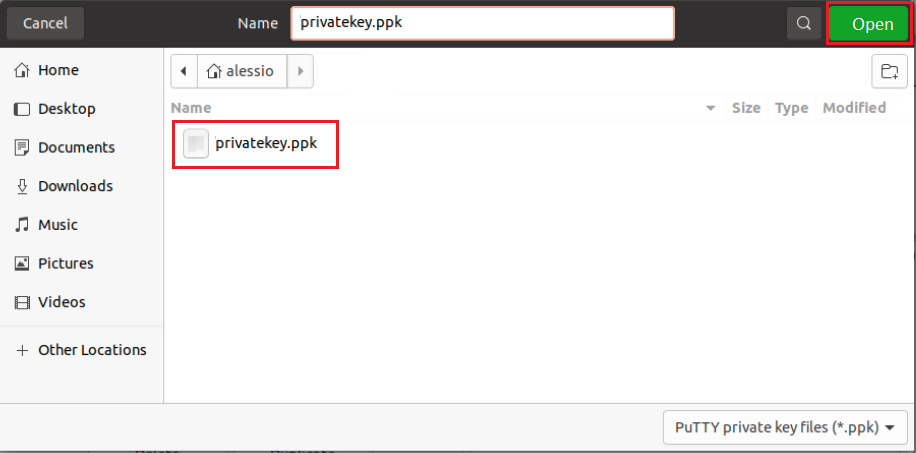
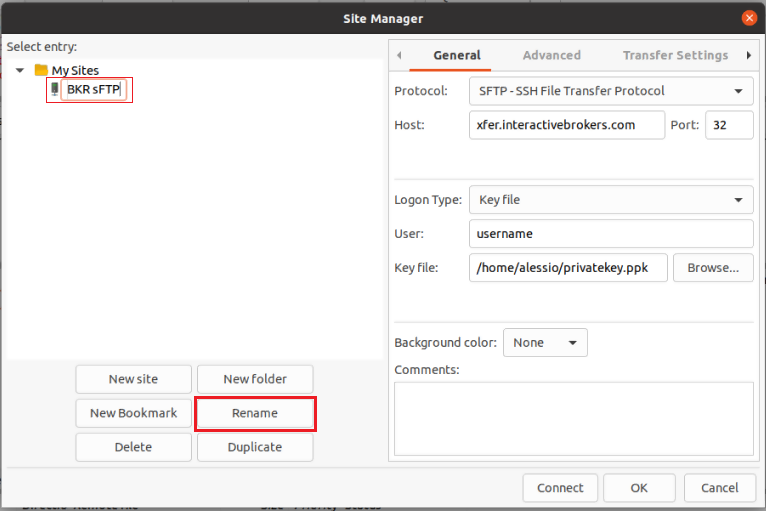
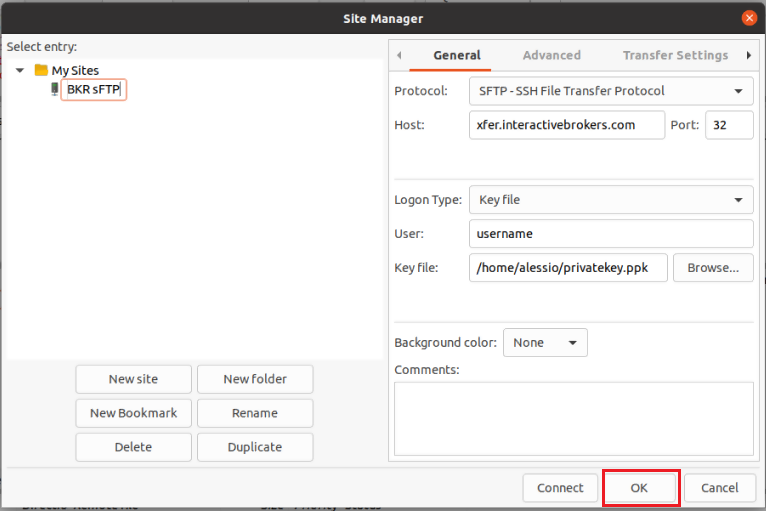
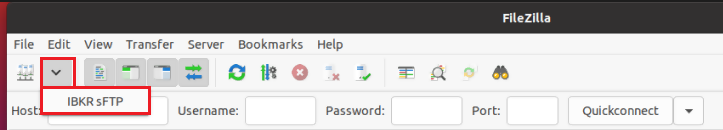
8. Click on the FileZilla top menu File -> Site Manager...
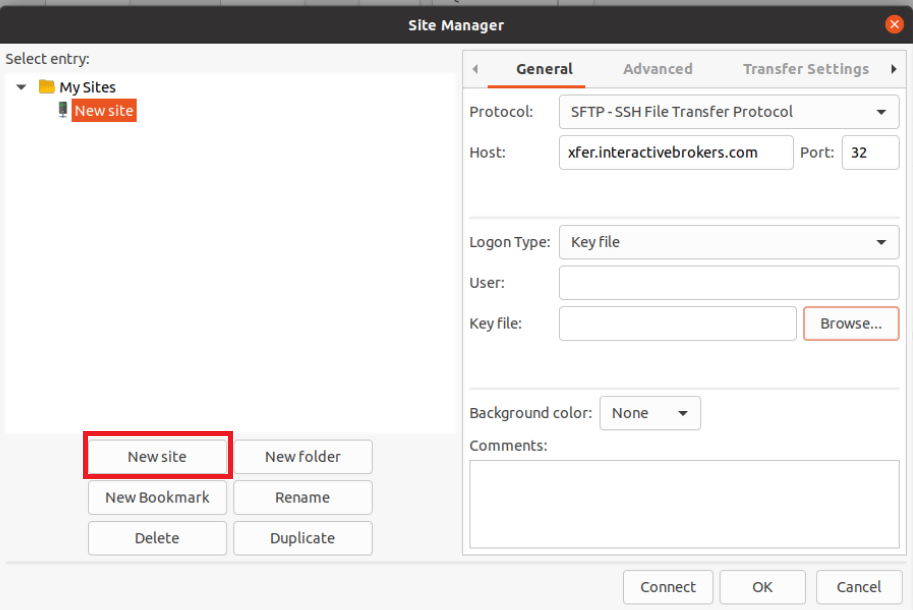
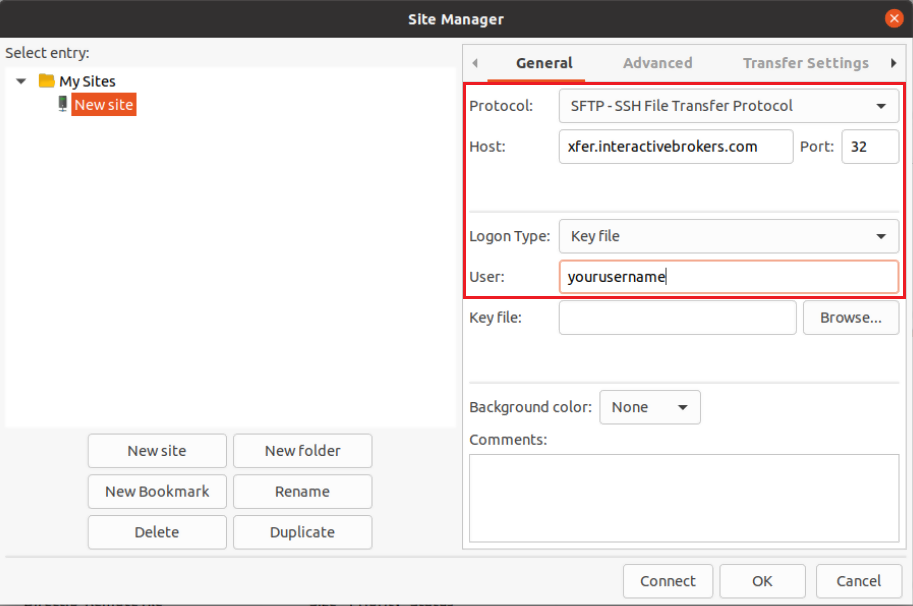
- Select SFTP - SSH File Transfer Protocol as Protocol
- Enter xfer.interactivebrokers.com in the Host field
- Enter 32 in the Port field
- Select Key file as Logon Type
- Enter the username provided to you by Interactive Brokers in the User field
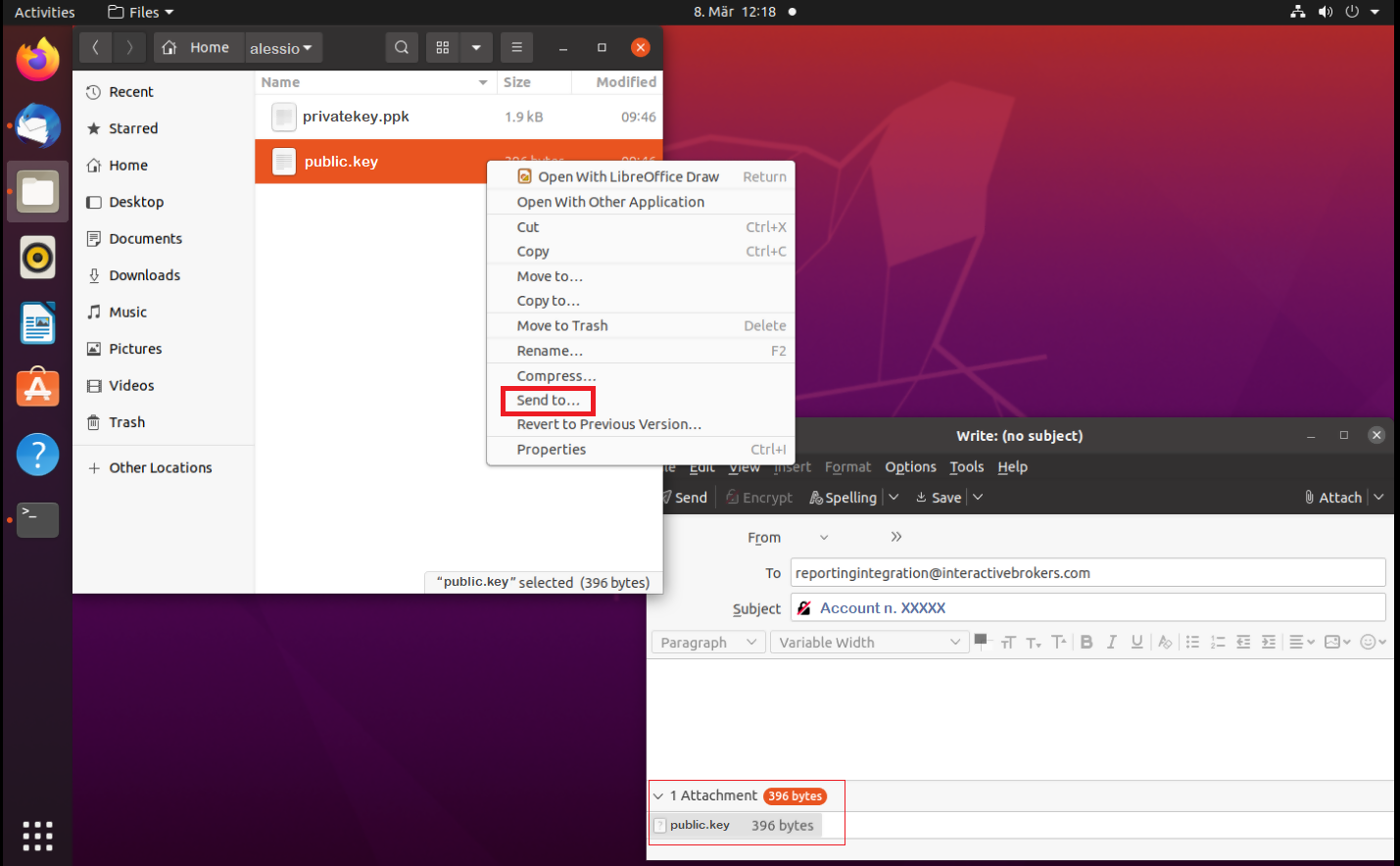
Important Note: do NOT send us your private key. Send us only your public one
Once IBKR has configured the parameters for your connection on our servers, you will be notified. After that, you will be able to access your sFTP repository by using the Site connection you have created in FileZilla. In case you have not yet set up a Site connection, please follow the steps from 6. to 14. which are a prerequisite to the below steps:

Common issues and solutions
-
Ensure the correct login details are being used to connect to the sFTP server. The username and password you are entering should match the ones you have received from the Reporting Integration Team.
-
Confirm you have configured your sFTP Client to use the Private Key file for the logon authentication (see steps 9. and 10. of the above procedure.)
-
Try accessing the sFTP server using a different Client (CyberDuck, ect.)
-
Ensure the Private Key file being used to Authenticate the server login attempt is related to the Public Key you originally sent to the Reporting Integration Team.
-
Should the above checks be unable to resolve the issue, please generate a new RSA Public/Private Key pair and send only the Public part to the Reporting Integration Team, as per IBKB3842.
-
In case you have an antivirus or a security software installed on your machine, make sure it is not blocking the FTP connection attempt. Normally, security software allows to set up exceptions for specific connections in order to whitelist them.
-
Verify that the public IP Address of the machine running the sFTP client, is the same you have originally provided to the Reporting Integration Team for being whitelisted. You can discover your public IP Address by searching the Internet for “what is my IP”. If your current IP Address is not the same you provided to us, please send it to our Reporting Integration Team for being whitelisted.
-
Ask your network administrator/s to confirm that your firewall allows both incoming and outgoing traffic from/to xfer.interactivebrokers.com on port TCP 32.
-
Should the above steps be unable to resolve the issue, please generate a new RSA Public/Private Key pair and send only the new Public part to our Reporting Integration Team, as per IBKB3842.
KB3968 - Generate a key pair using GPG for Windows
KB4205 - Generate a key pair using GPG Suite on macOS
KB4108 - Decrypt your Reports using GPG for Windows
KB4210 - Decrypting Reports using your PGP Key pair on macOS
KB4407 - Generate RSA Key Pair on Windows
KB4410 - How to set up sFTP for using Certificate Authentication on macOS
KB4411 - How to backup your public/private Key pair
KB4323 - How to transfer your public/private key pair from one computer to another
Exchange name change
Overview:
Interactive Brokers is completing an effort to update and consolidate exchange names where appropriate. When this effort is complete, the following updates will be in effect:
- GLOBEX and CMECRYPTO will be consolidated to a single exchange, ‘CME’
- ECBOT will be updated to ‘CBOT’
- COMEX listed metals (previously reflected as NYMEX) will be updated to exchange ‘COMEX’
- NYMEX, no change
Given the breadth of products involved, we are migrating in four waves based on underlying products:
| Key | Effective Trade Date | Products |
| Wave 1 | October 30, 2022 | GLOBEX: ZAR, LB, DA, IXE |
| Wave 2 | November 6, 2022 | GLOBEX: EMD, BRE, CHF, SOFR3, E7, NKD CMECRYPTO: BTCEURRR, ETHEURRR, MET |
| Wave 3 | November 13, 2022 | GLOBEX: All remaining products CMECRYPTO: All remaining products ECBOT: ZO, ZR, 2YY, 30Y NYMEX: ALI, QI, QC |
| Wave 4 | December 4, 2022 | ECBOT: All remaining products NYMEX: All remaining "Metal" products |
I am trading via API, how does this impact me?
For API clients the only requirement would be to provide a new exchange name, for example: exchange=”CME”, for existing contracts for the affected exchanges.
Old exchanges names will no longer be available after the change.
More details can be found within our FAQs through the following link: Upcoming Exchange name Changes
Note: If you are using a third party software connected to TWS or IB Gateway and that software does not recognize the new contract definitions, please contact the third party vendor directly.
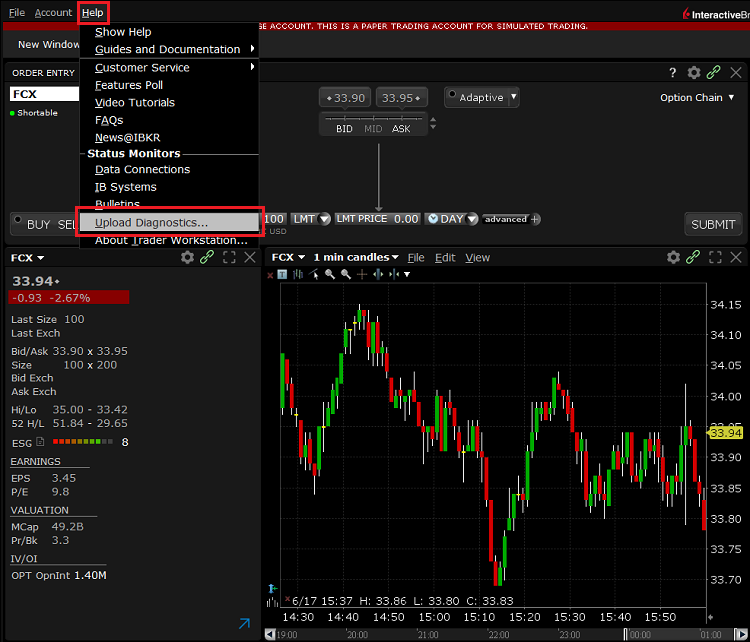
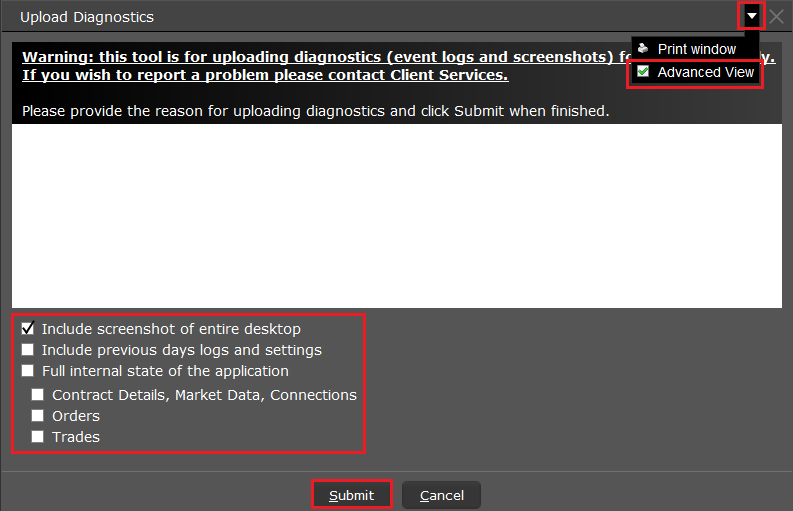
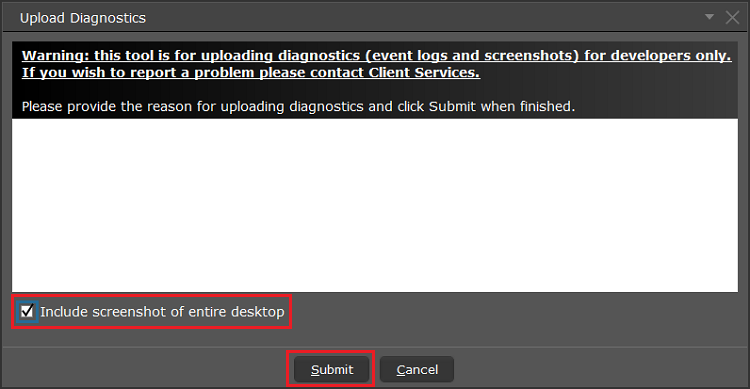
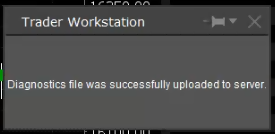
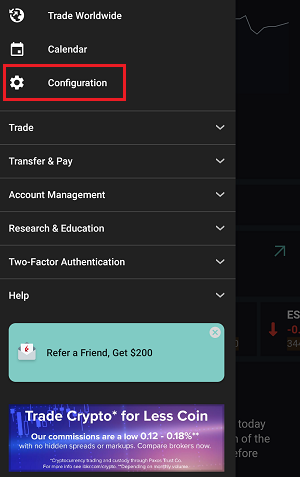
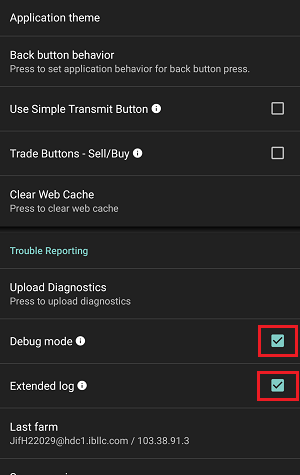
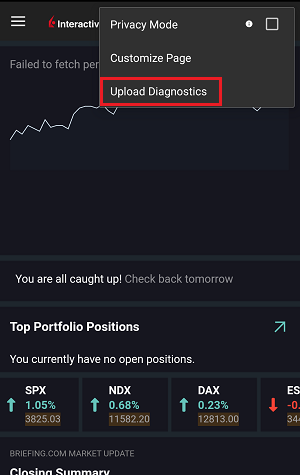
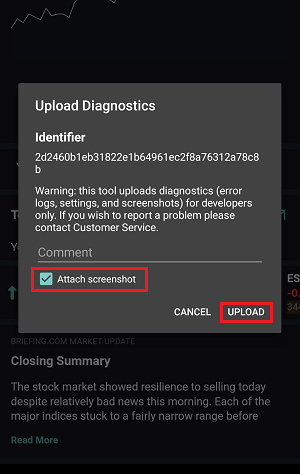
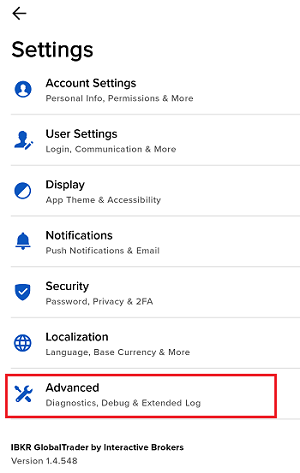
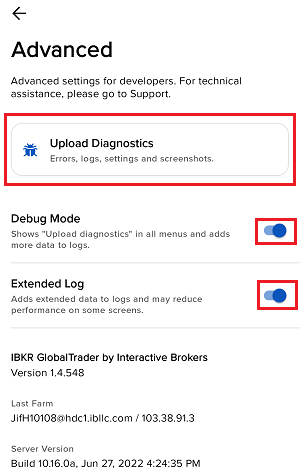
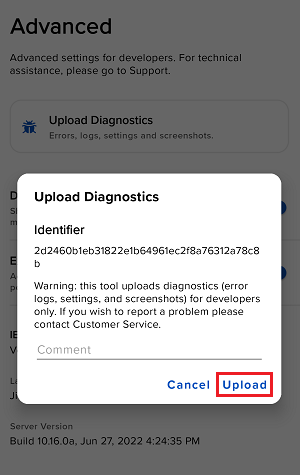
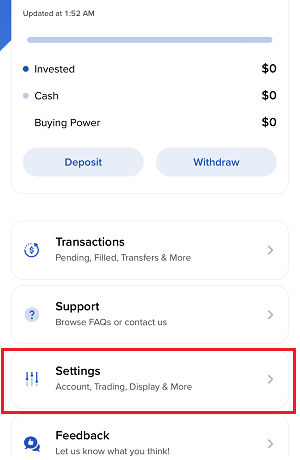
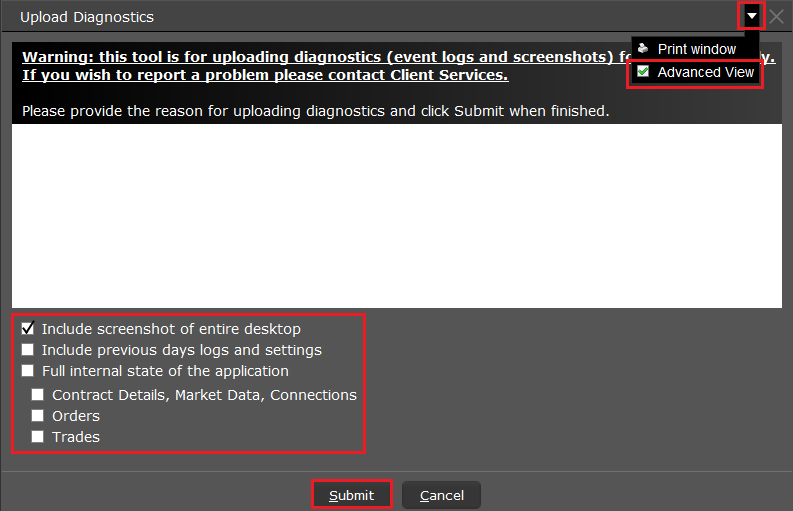
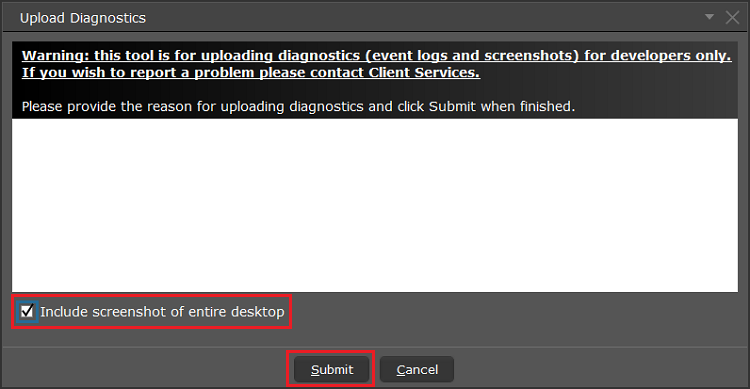
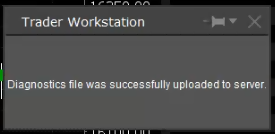
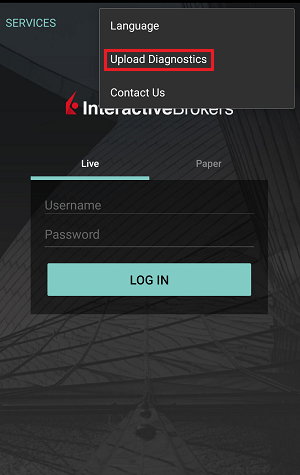
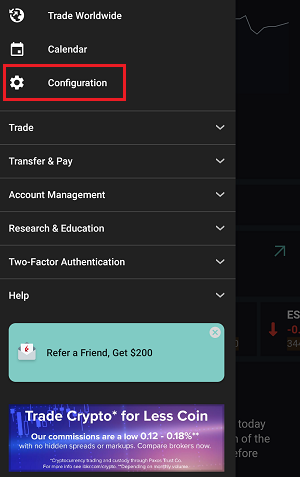
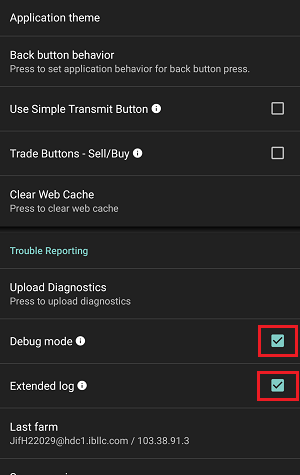
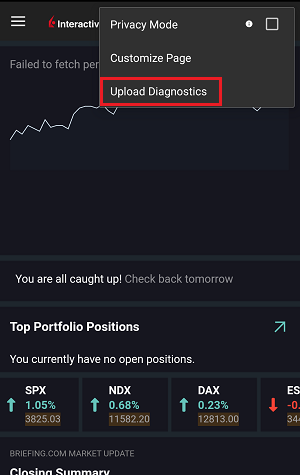
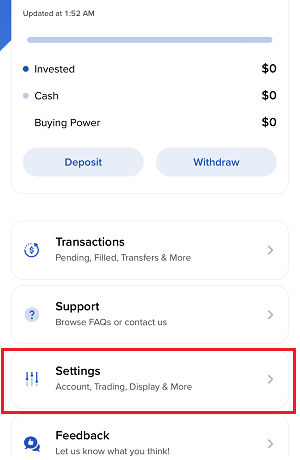
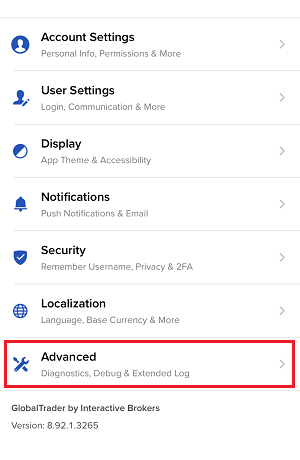
Как загрузить пакет диагностики через платформу IBKR
Некоторые ситуации требуют загрузки лог-файлов и скриншотов для нашей службы поддержки. Эта информация позволит нам лучше разобраться в Вашей проблеме и найти ей решение.
Данная статья содержит пошаговые инструкции по загрузке диагностических и лог-файлов через различные платформы Interactive Brokers.
Примечание: IBKR не следит за хранилищем пакетов диагностики. Если Вы вдруг решите загрузить пакет диагностики без запроса от Interactive Brokers, пожалуйста, проинформируйте нашу службу поддержки, создав тикет в "Центре сообщений" или позвонив нам, иначе Ваш отчет об ошибке не будет рассмотрен.
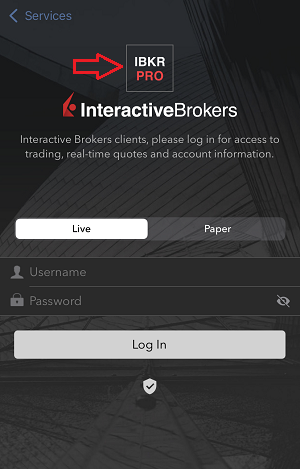
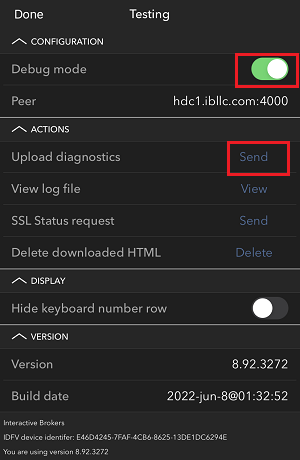
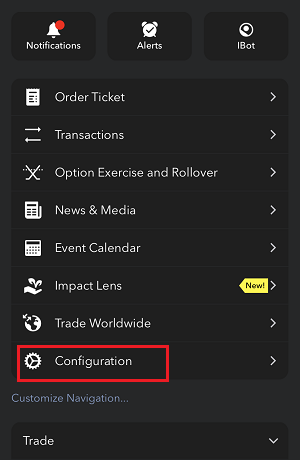
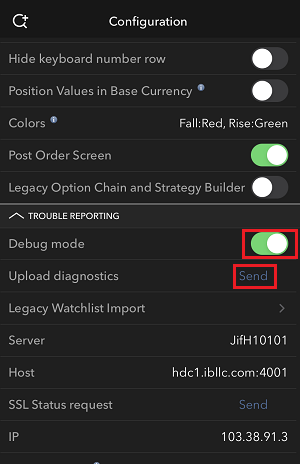
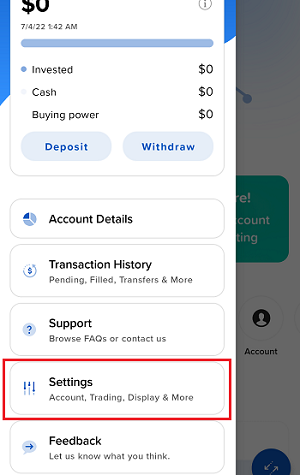
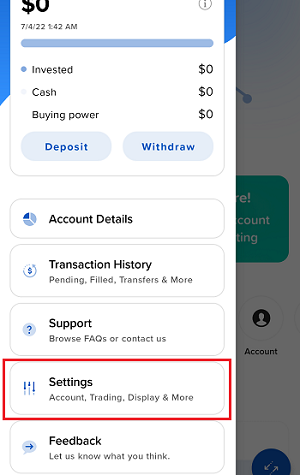
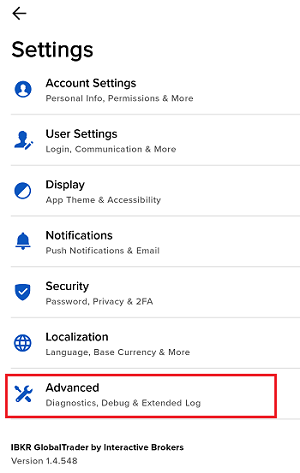
Перейдите по одной из ссылок ниже согласно используемой Вами платформе:
-
IBKR Mobile (Android)
-
IBKR Mobile (iOS)
- На ОС Windows и Linux: нажмите Ctrl+Alt+Q
- На Mac: нажмите Cmd+Option+H
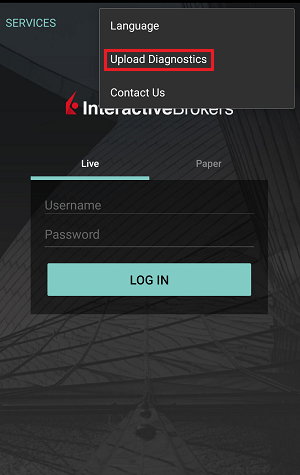
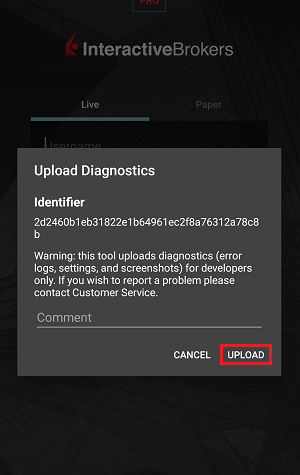
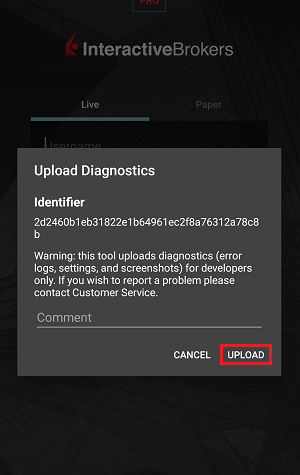
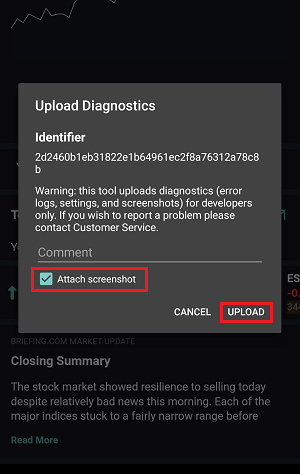
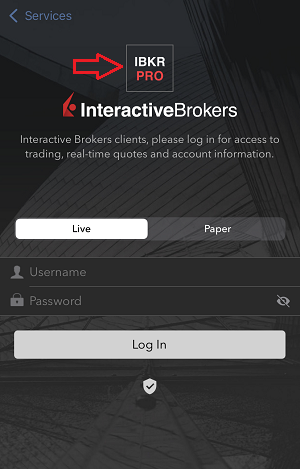
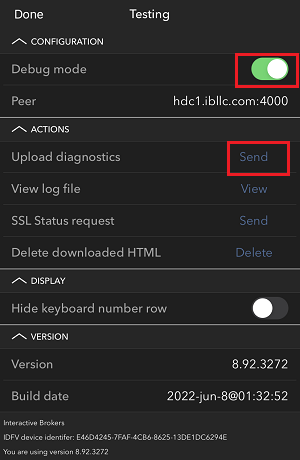
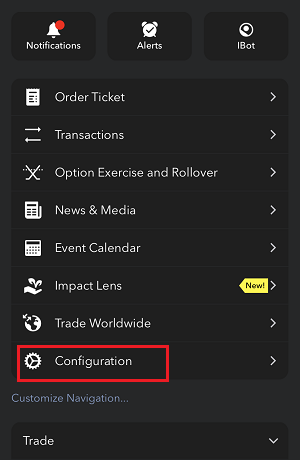
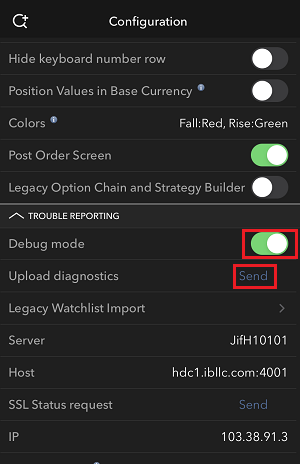
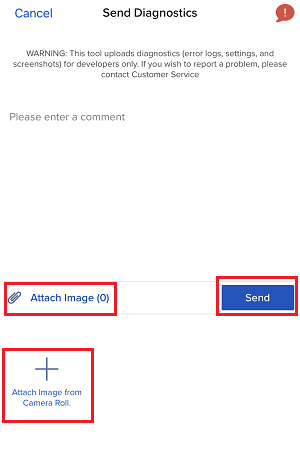
1. Быстро нажмите на логотип IBKR пять раз, чтобы открыть меню тестирования
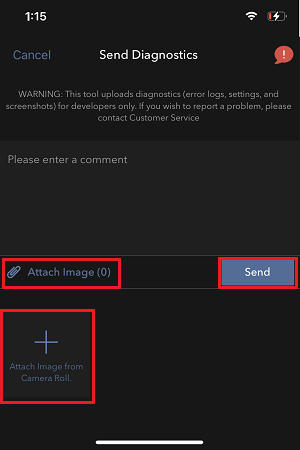
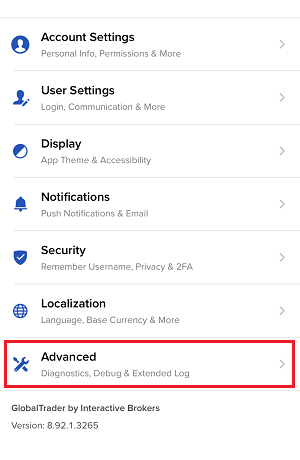
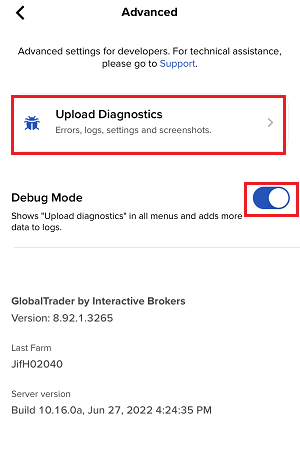
7. Введите свои комментарии в соответствующее поле и нажмите "Прикрепить изображение" (Attach Image), чтобы добавить сохраненные Вами в галерее скриншоты проблемы
Инструкция по созданию диагностического протокола для "Портала клиентов": IBKB3512
How to Upload a Diagnostic Bundle from an IBKR Platform
Some support related issues require diagnostics files and logs to be uploaded along with screenshots. The information will help our team to investigate and resolve the issue that you are experiencing.
This article will help you with detailed steps on how to upload diagnostics files and logs from various Interactive Brokers’ trading platforms.
Note: IBKR does not monitor the diagnostic bundle repository throughout the day. Should you spontaneously decide to upload a diagnostic bundle, without being instructed by Interactive Brokers, please inform our Client Services via Message Center ticket or phone call otherwise your error report will go unnoticed.
Please click on one of the links below, according to the platform you are using:
-
IBKR Mobile (Android)
-
IBKR Mobile (iOS)
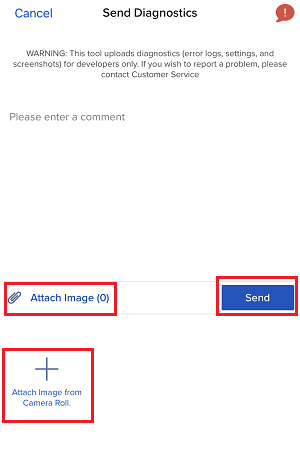
- For Windows and Linux Operating system: Press Ctrl+Alt+Q
- For Mac: Press Cmd+Option+H
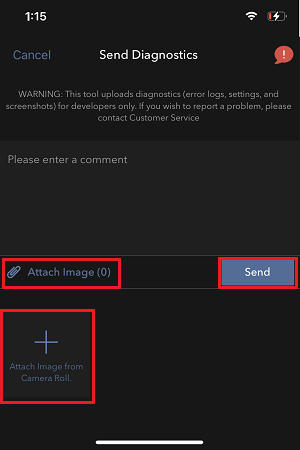
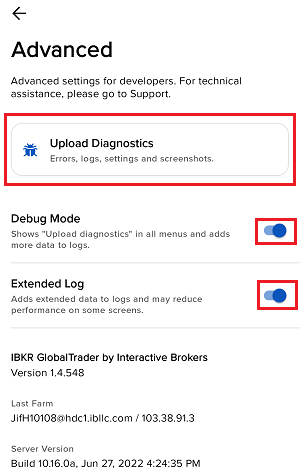
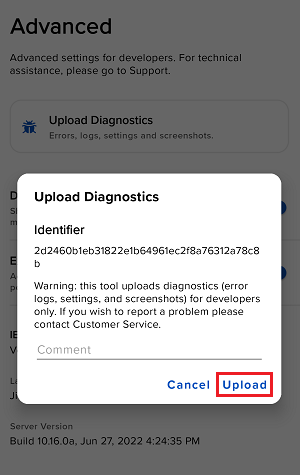
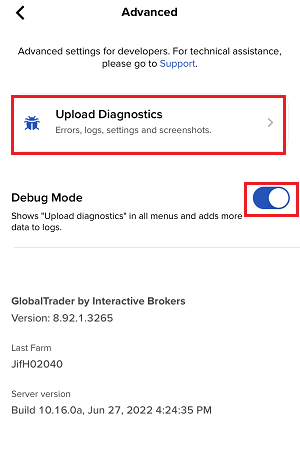
7. Enter your comments in the field and tap ‘Attach Image’ to attach the screenshot/s you previously saved in your camera roll
A diagnostic trace for Client Portal can be captured following the steps on IBKB3512
Как сгенерировать HAR-файл
Для решения нестандартных проблем нам иногда необходима дополнительная информация о работе Вашего браузера. Сотрудник поддержки может попросить Вас записать и прислать .har-файл. В данной файле содержится дополнительная информация о сетевых запросах, отправляемых и получаемых Вашим браузером. Чтобы сгенерировать файл, браузер записывает содержимое, время и статус запросов и ответов HTTP/HTTPS в момент возникновения проблемы.
Данная статья содержит инструкцию для генерирования .har-файла. Щелкните по браузеру, который Вы используете:
Чтобы сгенерировать файл HAR в Google Chrome:
1. Откройте Google Chrome и перейдите на страницу с ошибкой.
2. Нажмите CRTL +SHIFT + I на клавиатуре. Либо щелкните по иконке меню (три вертикальные точки в правом верхнем углу окна браузера) и выберите Дополнительные инструменты > Инструменты разработчика.
3. Сбоку или снизу экрана откроется панель инструментов разработчика. Откройте вкладку Сеть [Network] (изобр. 1).
Изобр. 1
.png)
4. В левом верхнем углу окна инструментов разработчика найдите круглую кнопку записи и проверьте, что она красного цвета. Если кнопка серого цвета, нажмите на нее один раз, чтобы начать запись, или просто нажмите CTRL+E (изобр. 2).
Изобр. 2
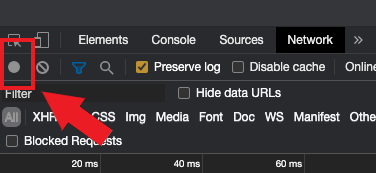
5. Установите флажок в поле Сохранять журнал [Preserve log] (изобр. 3).
Изобр. 3
.png)
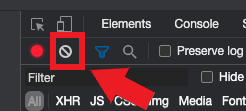
6. Нажмите на кнопку Сбросить, чтобы очистить старые журналы (значок в виде перечеркнутого круга справа от кнопки записи) (изобр. 4).
Изобр. 4
7. Воспроизведите ошибку, пока идет запись сетевых запросов.
8. Затем нажмите правой кнопкой мыши в любом месте в списке записанных сетевых запросов, выберите Сохранить все как HAR с содержимым и сохраните файл в папку на Ваш выбор (например, на рабочий стол).
9. На "Портале клиентов" IBKR откройте "Центр сообщений" и создайте тикет (или используйте старое обращение, если оно есть).
10. В тикете приложите сгенерированный .har-файл. Если служба поддержки IBKR сообщила Вам код тикета или имя сотрудника для обращения, укажите эту информацию в теле тикета.
11. Отправьте тикет.
Чтобы сгенерировать HAR-файл в Firefox:
1. Откройте Firefox и перейдите на страницу с ошибкой.
2. Нажмите F12 на клавиатуре. Либо щелкните по иконке меню (три параллельные горизонтальные линии в правом верхнем углу окна браузера) и выберите Веб-разработка > Сеть.
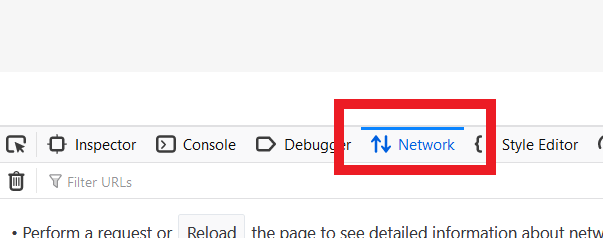
3. Сбоку или снизу экрана откроется панель инструментов разработчика. Откройте вкладку Сеть [Network] (изобр. 5).
Изобр. 5
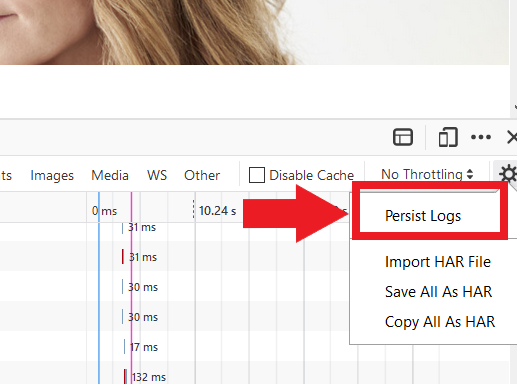
4. Установите флажок в поле Непрерывные логи [Persist logs] (изобр. 6).
Изобр. 6
5. Воспроизведите ошибку. Запись сетевых запросов начнется автоматически.
6. Затем нажмите правой кнопкой мыши в любом месте в списке записанных сетевых запросов и выберите Сохранить все как HAR.
7. Сохраните файл на компьютер (например, на рабочий стол).
8. На "Портале клиентов" IBKR откройте "Центр сообщений" и создайте тикет (или используйте старое обращение, если оно есть).
9. В тикете приложите сгенерированный .har-файл. Если служба поддержки IBKR сообщила Вам код тикета или имя сотрудника для обращения, укажите эту информацию в теле тикета.
10. Отправьте тикет.
Чтобы сгенерировать HAR-файл в Microsoft Edge:
1. Откройте Edge и перейдите на страницу с ошибкой.
2. Нажмите F12 на клавиатуре. Либо щелкните по иконке меню (три горизонтальные точки в правом верхнем углу окна браузера) и выберите Другие инструменты > Средства разработчика.
3. Откройте вкладку Сеть [Network] (изобр. 10).
Изобр. 10
.png)
4. Воспроизведите ошибку, пока идет запись сетевых запросов.
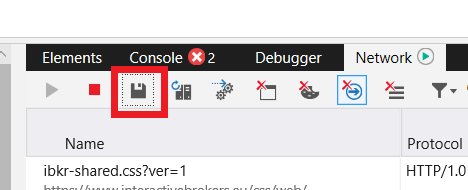
5. Затем нажмите на иконку дискеты (Экспортировать как HAR) или нажмите CTRL+S (изобр. 11).
Изобр. 11
6. Введите имя файла и выберите, куда хотите его сохранить (например, на рабочий стол). Нажмите Сохранить.
7. На "Портале клиентов" IBKR откройте "Центр сообщений" и создайте тикет (или используйте старое обращение, если оно есть).
8. В тикете приложите сгенерированный .har-файл. Если служба поддержки IBKR сообщила Вам код тикета или имя сотрудника для обращения, укажите эту информацию в теле тикета.
9. Отправьте тикет.
Чтобы сгенерировать HAR-файл в Safari:
Примечание. Перед генерацией HAR-файла убедитесь, что в меню Safari отображается вкладка "Разработка" (Develop). Если вкладка не отображается, нажмите на меню Safari, откройте "Настройки" (Preferences), нажмите "Дополнения" (Advanced) и установите флажок в поле "Показывать меню "Разработка" в строке меню" (Show Develop menu in menu bar).
1. Щелкните по вкладке Разработка и выберите Показать веб-инспектор или нажмите CMD+ALT+I.
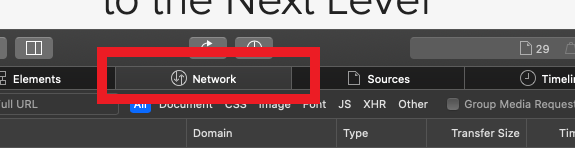
2. Откройте вкладку Сеть [Network] (изобр. 12).
Изобр. 12
3. Установите флажок в поле Сохранить журнал [Preserve log] (изобр. 13).
Изобр. 13
.png)
4. Щелкните по иконке экспорта (или нажмите CMD+S), введите имя файла, выберите место на компьютере (например, рабочий стол) и сохраните .har-файл.
5. На "Портале клиентов" IBKR откройте "Центр сообщений" и создайте тикет (или используйте старое обращение, если оно есть).
6. В тикете приложите сгенерированный архив. Если служба поддержки IBKR сообщила Вам код тикета или имя сотрудника для обращения, укажите эту информацию в теле тикета.
7. Отправьте тикет.
Generate RSA Key Pair on Windows
These instructions apply to users who are receiving their statements via sFTP. If you elected to receive your statements via sFTP, you would first need to generate an RSA Key pair.
To generate an RSA Key pair:
2. Run the installer and make sure to check PuTTYgen (key generator) as one of the components to install.
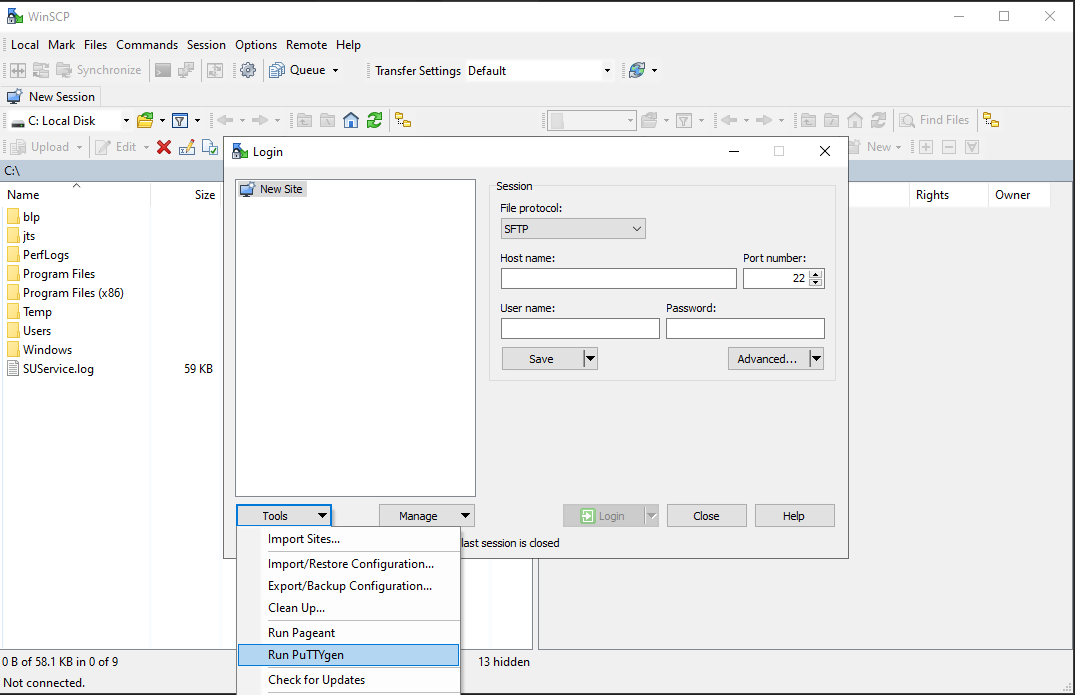
3. Start WinSCP and from the button Tools select Run PuTTYgen.
4. Once the tool PuTTYgen has been launched, click Generate. Select RSA as Type of key to generate, 2048 as Number of bits in generated key and click on the button Generate.
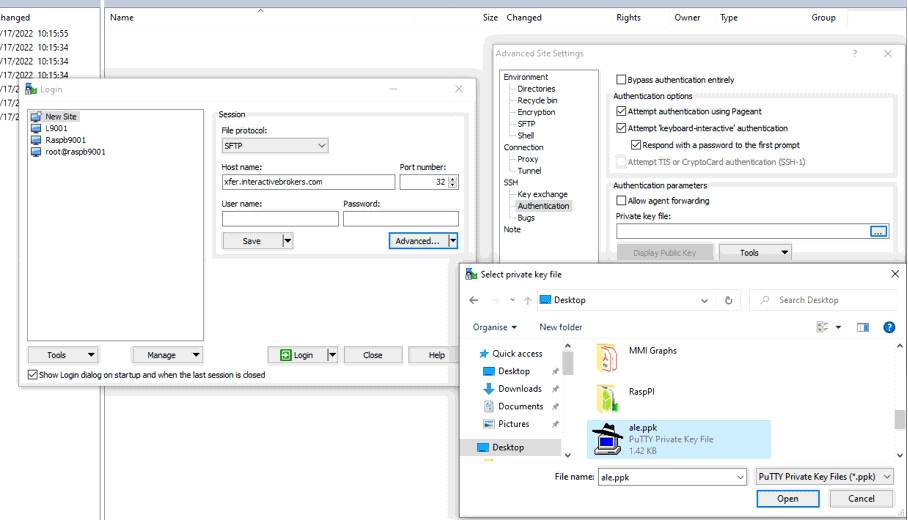
5. Click "Save private key" and give the file a name (like private). Leave the extension as .ppk ('ale.ppk', in the picture below is an example filename).
Important Note: do NOT save your public key yet. Save only your private one.
.png)
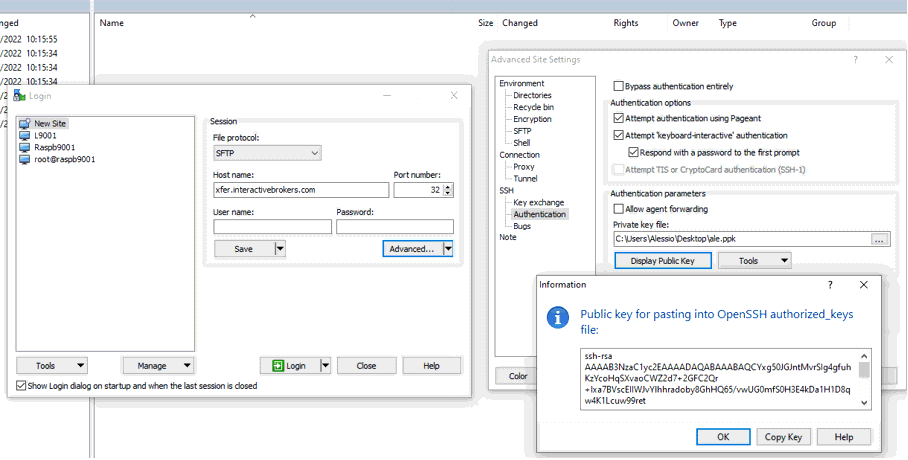
6. Open WinSCP, create a new connection and:
- Select SFTP as File protocol.
- Enter xfer.interactivebrokers.com in the Host name field.
- Enter 32 in the Port number field.
8. In the Advanced Site Settings screen, left side menu, expand SSH and select Authentication. Click on the button ... at the end of the field Private Key file and open the private key you previously saved at point 5):
9. Click on the button Display public key:
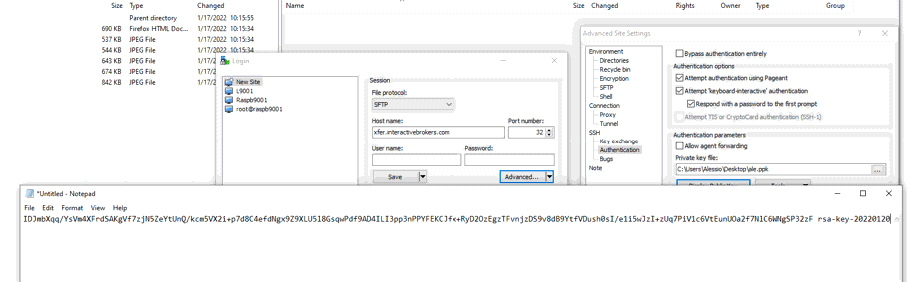
11. Open Notepad, press CTRL+V to paste the key string (which is one string of characters without spaces) and then save the file with the name public.key in a folder of your preference:
12. Send the file you saved at the previous step to us via Message Center ticket or email as per instructions on IBKB3842
KB3842 - Using GPG/RSA encryption keys to guarantee the privacy and security of your Reports
KB3968 - Generate a key pair using GPG for Windows
KB4205 - Generate a key pair using GPG Suite on macOS
KB4108 - Decrypt your Reports using GPG for Windows
KB4210 - Decrypting Reports using your PGP Key pair on macOS
Transferring your Key Pair From One Computer To Another
If you need to decrypt files that were encrypted with your private Key on an additional computer, you need to copy both your private and public keys (the entire Key pair) to that computer.
Note: this tutorial assumes you have already set up a Key pair. If you need guidance to set up the Key pair please refer to this article, which is a prerequisite to the instructions below.
How to transfer your Key pair:
Please select one of the below links, according to your Operating System:
Windows
1. On the machine where the encryption keys are stored, connect a USB drive to a free USB port.
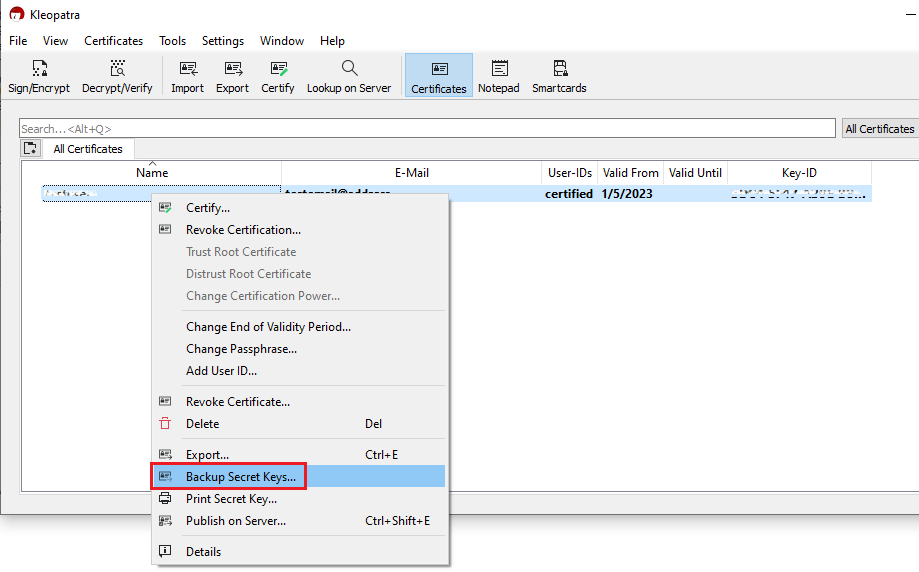
2. Launch the Kleopatra application and select the encryption key you want to transfer. Then right-click on the selection and choose Backup Secret Keys...
Note: Do NOT use Export..., as this will only export the public part of the Key while you need to have a backup of both public and private parts.
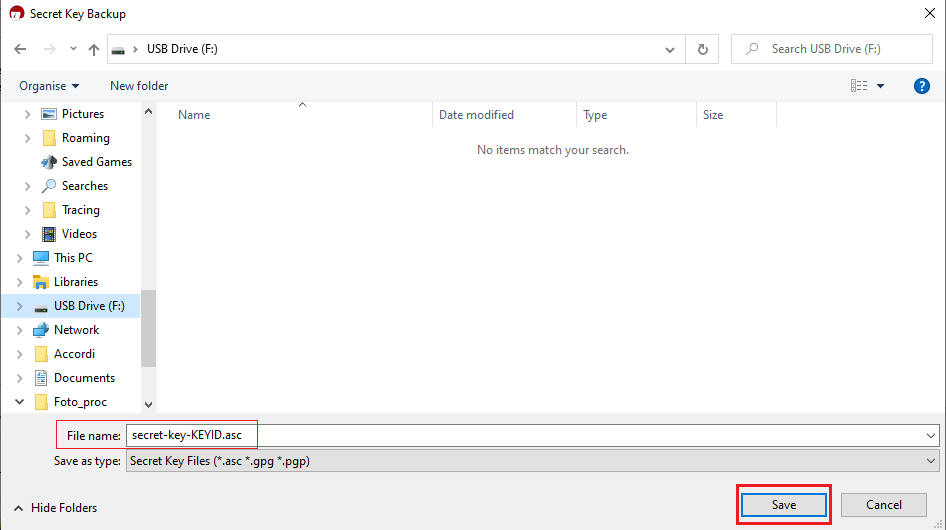
3. Select your USB drive as destination and a filename of your preference (e.g. secret-key-KEYID.asc) for your backup copy. Then click Save.
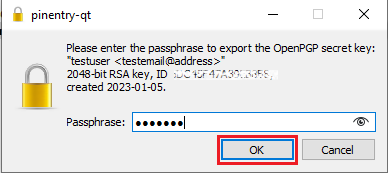
4. Enter the passphrase you have set when you created the Key and click OK.
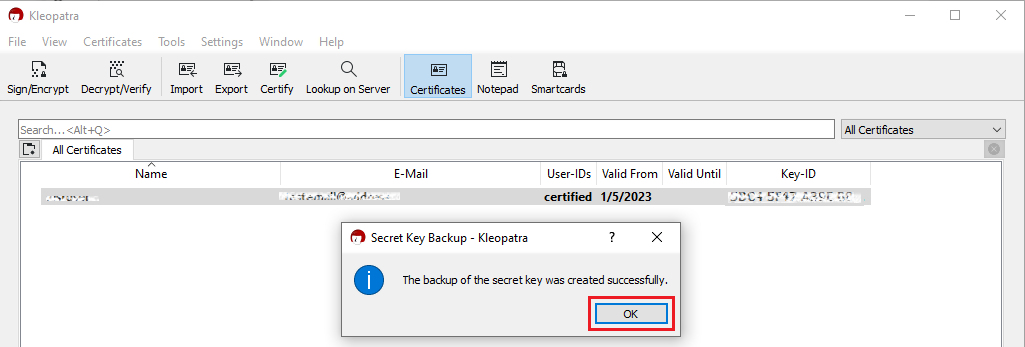
5. A pop-up will confirm the backup has been successfully created. Click OK.
6. Eject your USB drive safely through the Windows interface to prevent data loss and connect it to a free USB port on the other computer (the one you want to transfer the key to). All the next steps have to be executed on that machine.
7. Make sure the the GPA software is installed, otherwise please install it. Make sure that the component Kleopatra is selected as one of the sub components to include in the installation.
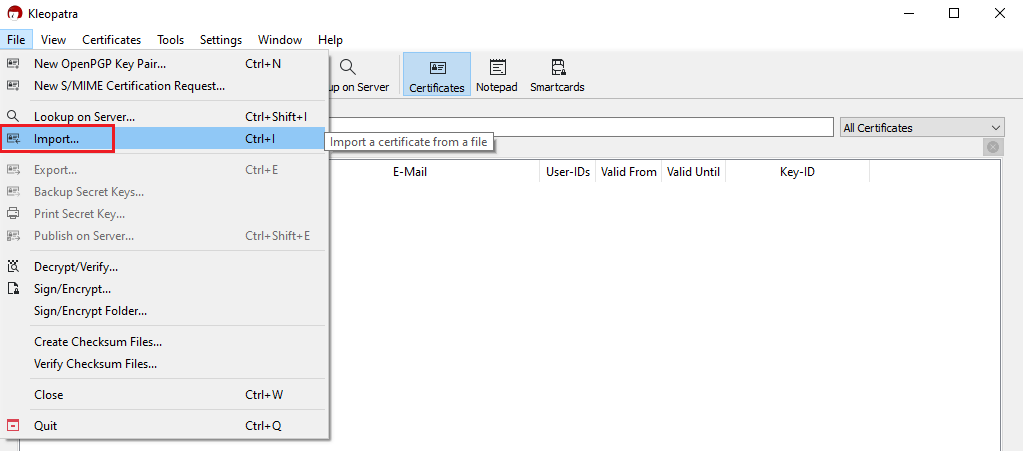
8. Launch the Kleopatra application and click on the top menu File and select Import...
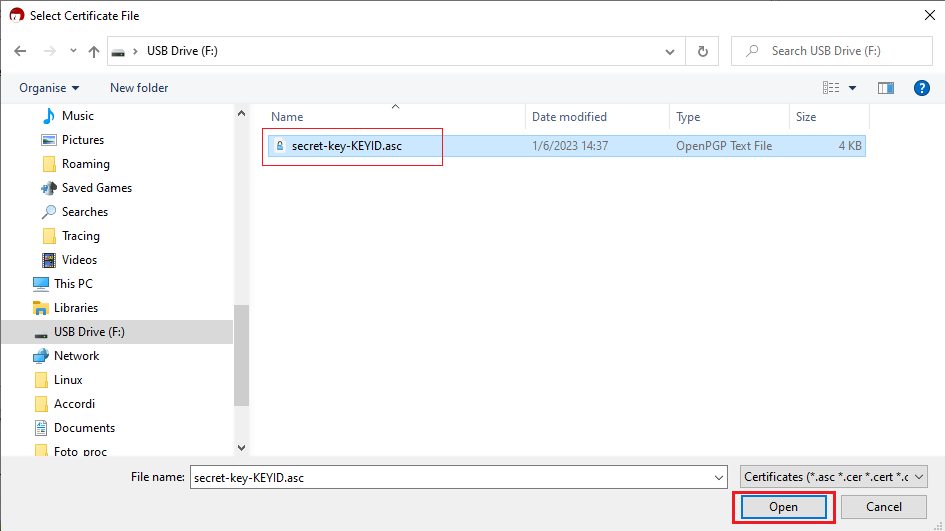
9. Click on the letter correspondent to your USB drive and select the file you have previously saved (e.g. secret-key-KEYID.asc). Then click Open.
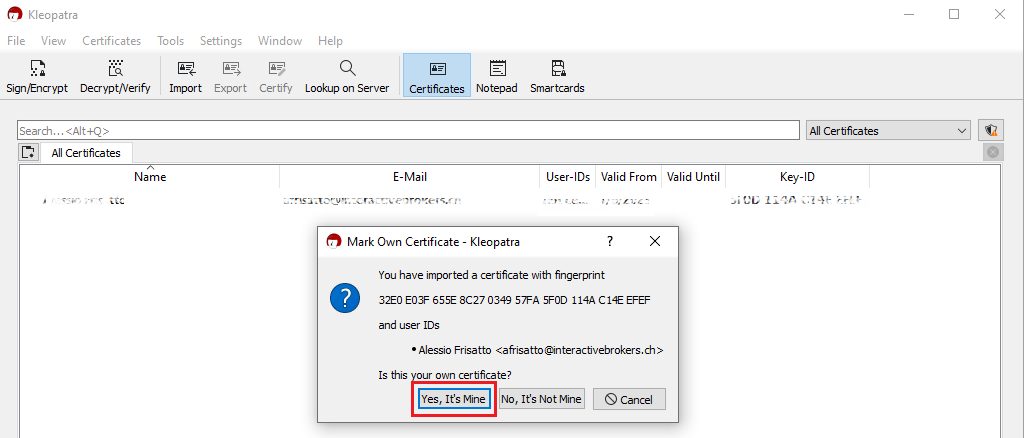
10. Click on Yes, It's Mine.
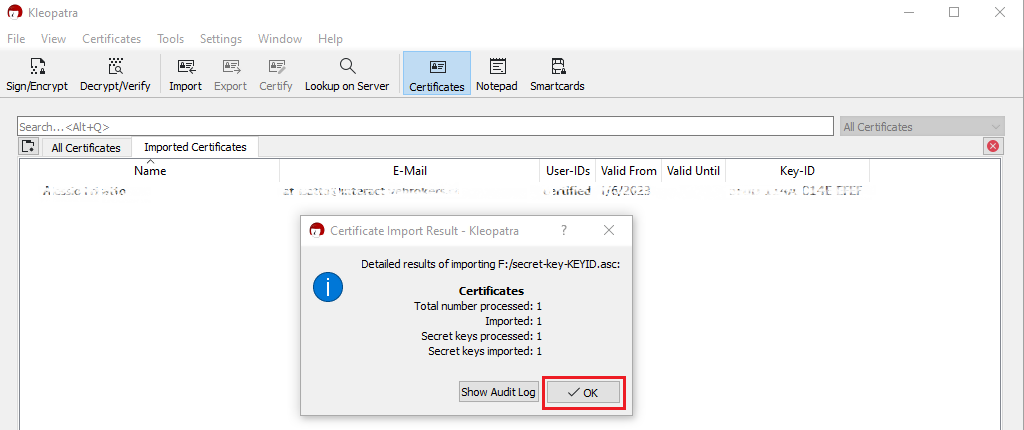
11. A pop-up will confirm the Key has been successfully imported. Click OK. You may now want to delete the key file from the USB drive and empty the Trash.
macOS
1. On the machine where the encryption keys are stored, connect a USB drive to a free USB port.
2. Launch the GPG Keychain application and select the encryption key you want to transfer. Please make sure that you see the text Type: Secrete and public key, in the Type column.
.png)
3. With the desired encryption key highlighted, click Export. Please make sure to check the box for the option Include secret key in exported file, as illustrated in the above screenshot. Save the key pair to the USB drive.
4. Eject the USB drive and connect it to a free USB port on the other computer (the one you want to transfer the key to). All the next steps have to be executed on that machine.
5. Make sure the GPG Tools suite is installed, otherwise please install it.
6. Launch the GPG Keychain application and click the icon Import on the top toolbar.
(1).png)
7. Click the USB Drive and select the previously saved .ASC file that contains the Public and Private key. Then click Open.
8. The confirmation should read Import successful.
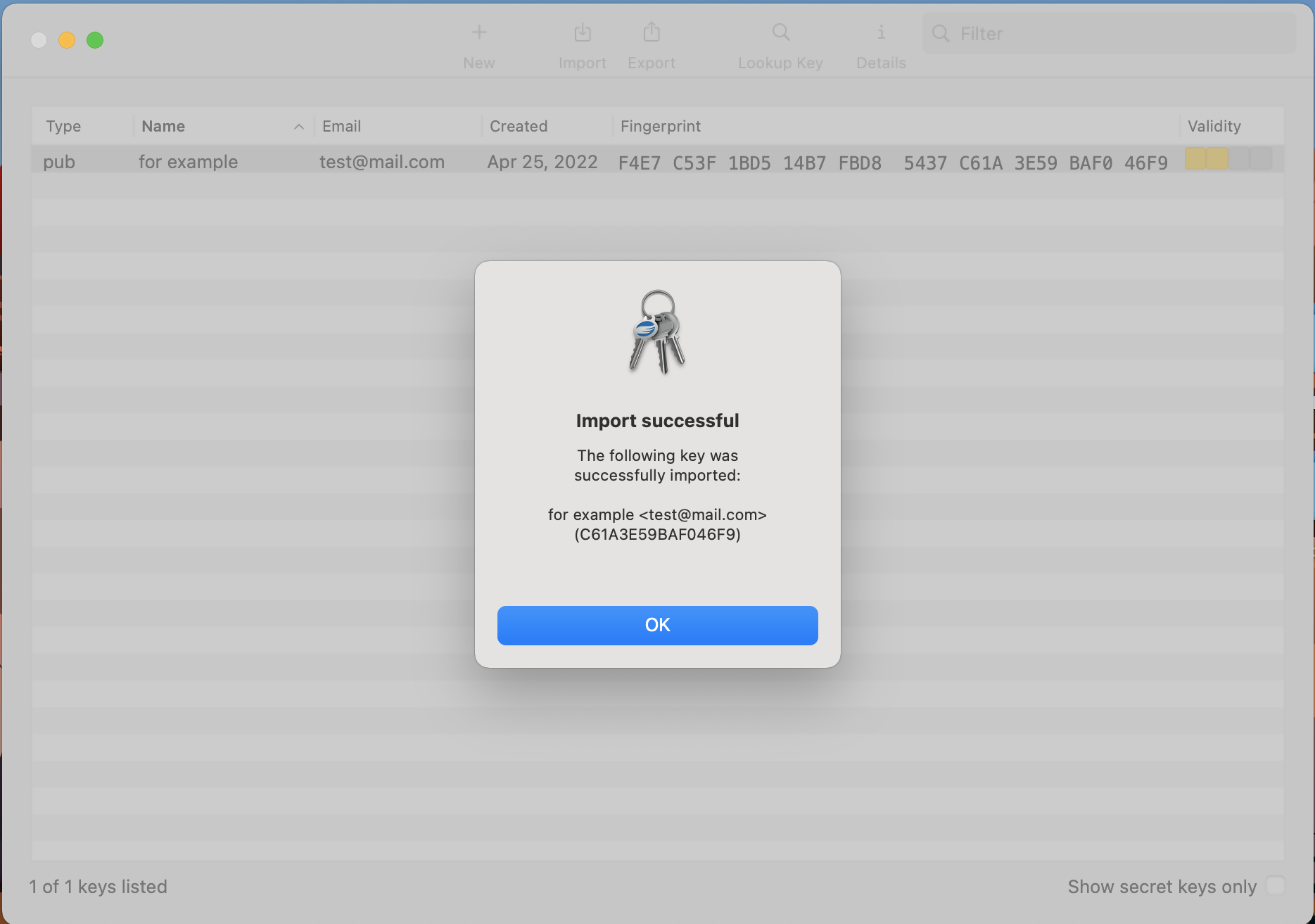
9. Once the key has been successfully imported, delete the key file from the USB drive and empty the Trash.
KB3842 - Using GPG/RSA encryption keys to guarantee the privacy and security of your Reports
KB3968 - Generate a key pair using GPG for Windows
KB4205 - Generate a key pair using GPG Suite on macOS
KB4108 - Decrypt your Reports using GPG for Windows
KB4210 - Decrypting Reports using your PGP Key pair on macOS
KB4407 - Generate RSA Key Pair on Windows
Аутентификация через IBKR Mobile (IB Key) без уведомлений
Если отправка уведомлений от IBKR Mobile на телефон невозможна, Вы можете авторизоваться с помощью метода с проверочным и ответным кодом, описанного на страницах ниже (в зависимости от операционной системы Вашего устройства):
Эти же инструкции действуют в случаях, когда на телефоне нет доступа к интернету (в роуминге, нет сети, интернет не подключен и т.д.)
Если доступ к интернету есть, но на телефон не приходят уведомления от IBKR Mobile, следуйте инструкциям в данной статье.
Decrypting Reports Using Your PGP Key Pair on macOS
Note: This tutorial assumes you received reports via email or via FTP that were encrypted with the public key you sent to IBKR . If you need guidance to set up the encrypted statement delivery, please refer to this article, which is a prerequisite to the instructions below.
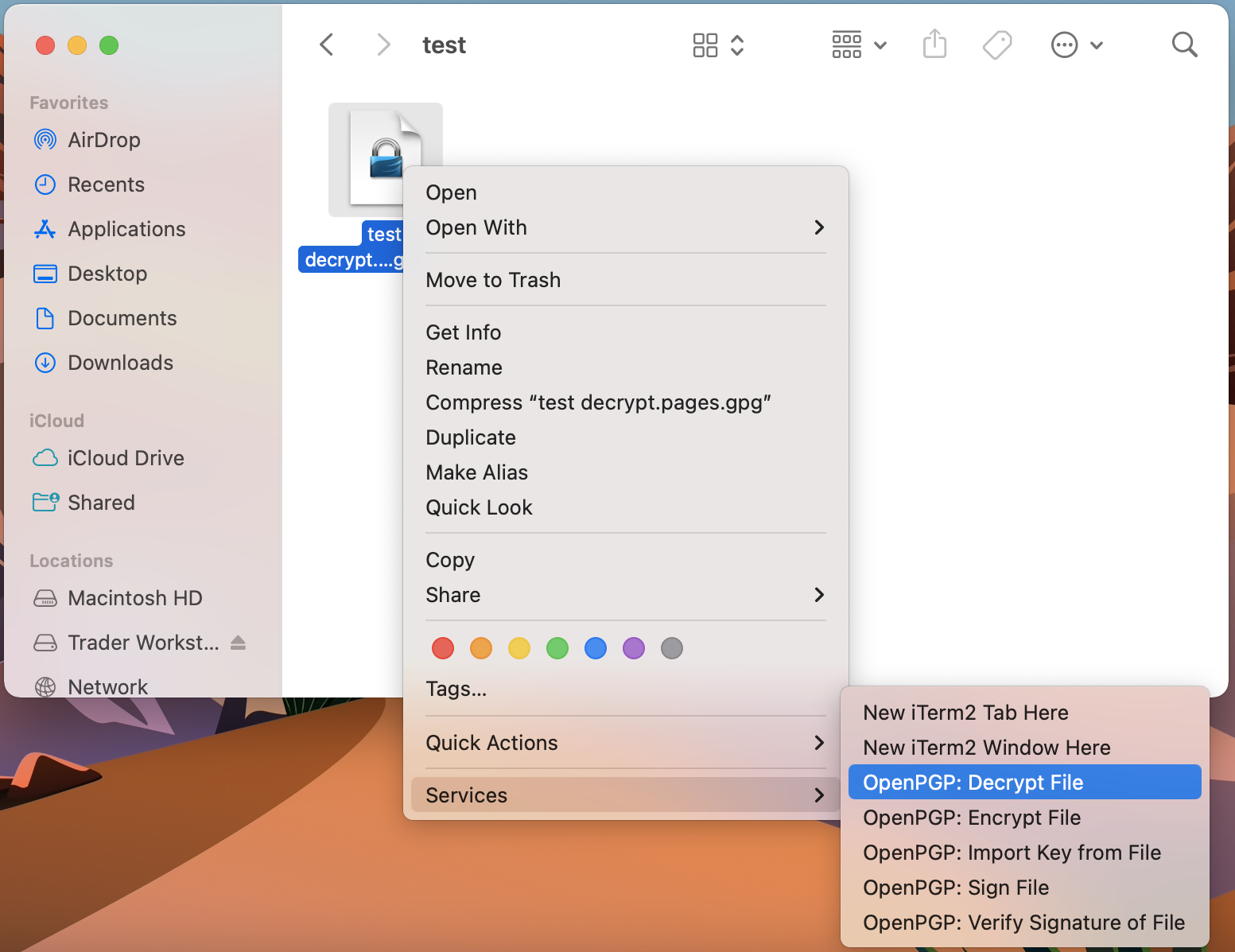
1. Open Finder
2. Right click on the .gpg file you want to decrypt
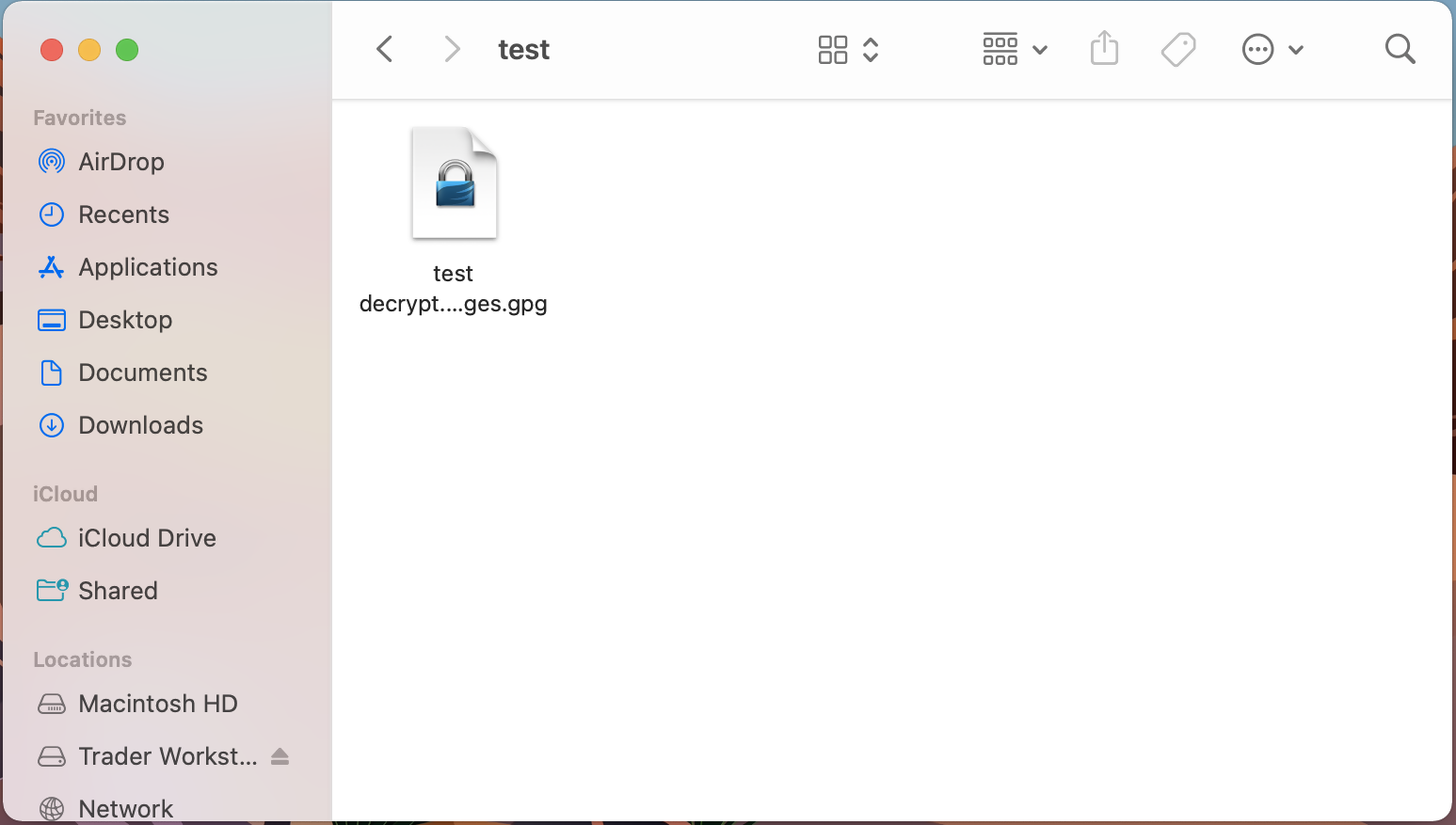
3. Select Services > OpenPGP: Decrypt File
Common Issues/Questions
- Decryption failed with error 'No Secret Key'
This is commonly caused when the wrong encryption key is used to decrypt the file. If decryption is being done on a computer other than the original computer used to create the public/private keys, the keys would have to be transferred from the original computer to the new computer.
If the above does not help, then a new public/private key pair needs to be created and sent to us.
KB3842 - Using GPG/RSA encryption keys to guarantee the privacy and security of your Reports
KB3968 - Generate a key pair using GPG for Windows
KB4205 - Generate a key pair using GPG Suite on macOS
KB4108 - Decrypt your Reports using GPG for Windows
KB4407 - Generate RSA Key Pair on Windows
Decrypt Your Reports Using GPG for Windows
Note: This tutorial assumes you received reports via email or via FTP that were encrypted with the public key you sent to IBKR. If you need guidance to set up the encrypted statement delivery, please refer to this article, which is a prerequisite to the instructions below.
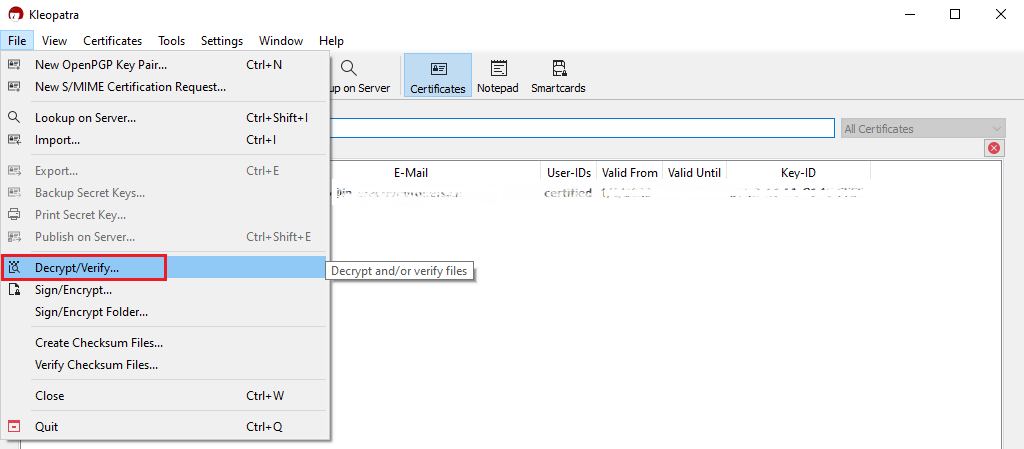
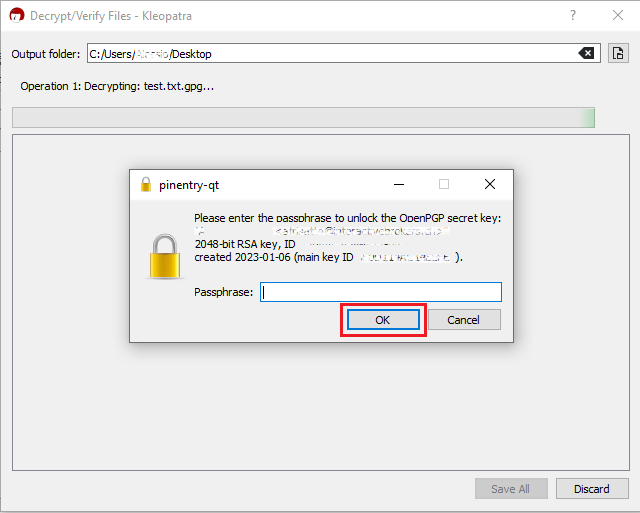
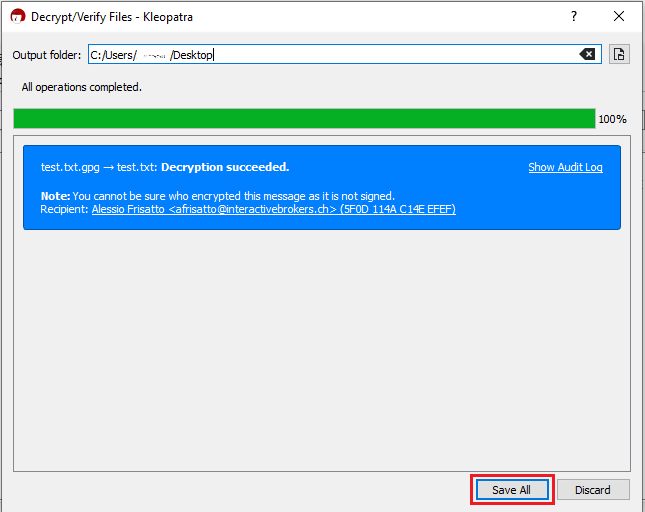
How to decrypt files using Kleopatra:
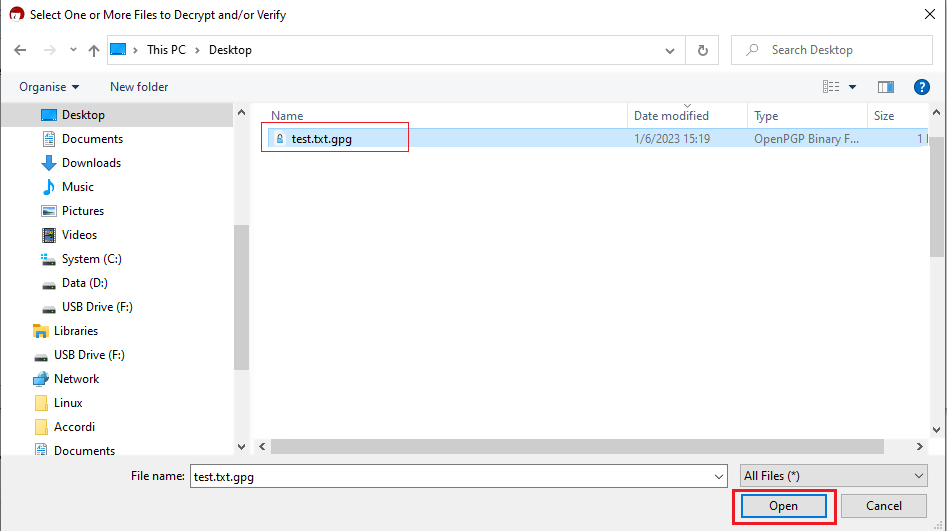
1. Save all the encrypted Reports you received via email or FTP in a folder on your preference (e.g. Desktop)
2. Start the Kleopatra application (included in Gpa4win software). The entry for your Key should be listed in the All Certificates panel. Click the top menu File and select Decrypt/Verify...

Common Issues/Questions
- Decryption failed with error 'No Secret Key'
This is usually caused by the wrong encryption key being used to decrypt the file. If decryption is being done on a computer other than the original computer used to create the public/private keys, the keys would have to be transferred from the original computer to the new computer.
If the above does not help, then a new public/private key pair needs to be created and sent to us.
KB3842 - Using GPG/RSA encryption keys to guarantee the privacy and security of your Reports
KB3968 - Generate a key pair using GPG for Windows
KB4205 - Generate a key pair using GPG Suite on macOS
KB4210 - Decrypting Reports using your PGP Key pair on macOS
KB4407 - Generate RSA Key Pair on Windows
KB4409 - How to set up sFTP for using Certificate Authentication on Windows
KB4410 - How to set up sFTP for using Certificate Authentication on macOS
KB4411 - How to backup your public/private Key pair
KB4323 - How to transfer your public/private key pair from one computer to another